Indirect Prompt Injection Is Live in the Wild — Google + Forcepoint Reports Reveal 10 Payload Families
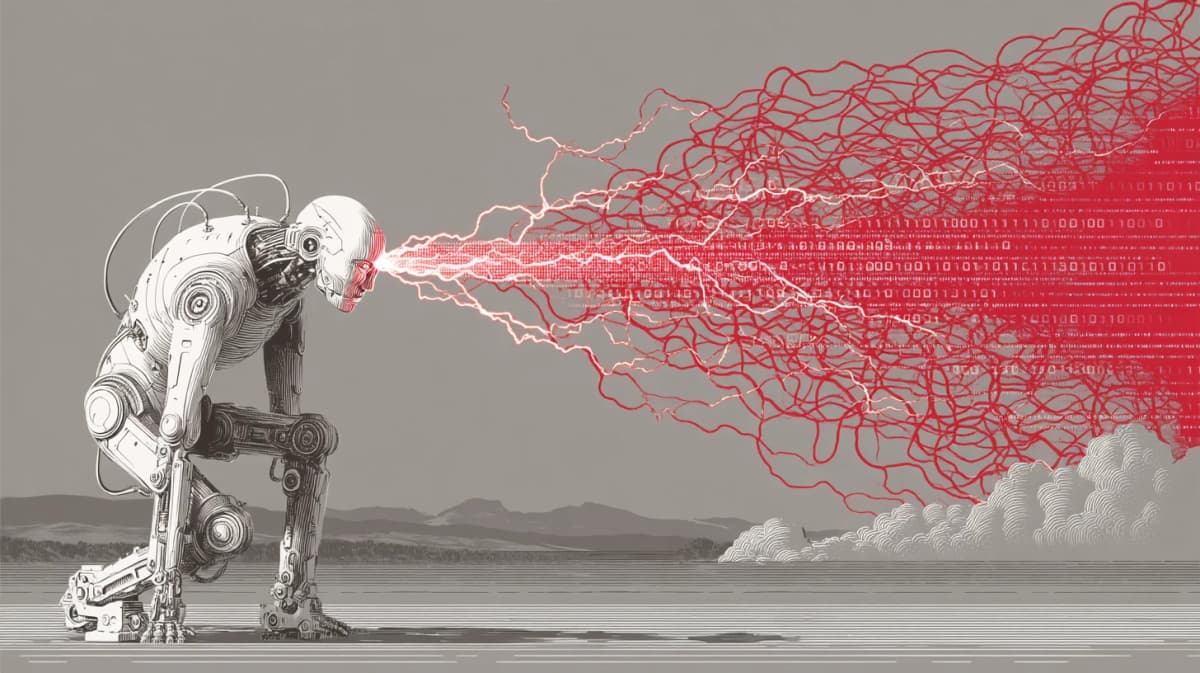
An AI agent reads an email. Hidden inside the email body, invisible to human eyes, is a single line of text that hijacks the agent and redirects a wire transfer. This is not a thought experiment anymore.
10 Payloads
On April 24, 2026, Google's Online Security Blog and Forcepoint X-Labs independently published reports on indirect prompt injection attacks observed in the wild. Google analyzed patterns found across 2-3 billion pages crawled monthly. Forcepoint cataloged 10 distinct payload families actively circulating on the open internet. Both reports arrive at the same conclusion: indirect prompt injection has graduated from proof-of-concept to operational attack vector.
The reports have been sitting on the Hacker News front page for over a week. That alone says something. This is not just a security niche topic anymore -- it strikes at the foundation of every AI agent architecture that processes external content.
From Lab to Battlefield
Indirect prompt injection is fundamentally different from the direct kind. In a direct attack, the attacker types something malicious straight into the AI. In an indirect attack, the attacker plants instructions inside content that the AI will later consume -- emails, web pages, PDFs, spreadsheets, calendar invites. The attacker never touches the AI directly. They poison the well and wait.
This distinction matters because it changes the threat model entirely. Direct injection requires access to the AI interface. Indirect injection requires nothing more than the ability to send someone an email or publish a web page. The attack scales effortlessly. One poisoned page can compromise every AI agent that reads it.
Until late 2025, the security community treated this as a theoretical concern. Princeton researchers demonstrated that Bing Chat would follow hidden instructions on web pages. Academic papers outlined attack taxonomies. Red teamers built proof-of-concept demos at DEF CON. But the consistent caveat was always the same: "no confirmed in-the-wild exploitation."
Google's April 2026 report removed that caveat. Their web crawler, which processes 2-3 billion pages every month, found injection payloads embedded in live web pages -- and the numbers are trending up.
Google's Data -- 32% Increase Across 2.3 Billion Pages
The headline number from Google's report is a 32% increase in malicious injection patterns between November 2025 and February 2026. At the scale Google operates -- billions of pages per month -- even a small percentage increase represents a meaningful absolute number.
Google categorized the observed patterns into several types. The most common is system prompt tag impersonation: injecting strings like [SYSTEM] or <|im_start|>system into web page content so that AI models mistake them for legitimate system-level instructions. Meta namespace spoofing is a related technique, abusing HTML <meta> tags to slip instructions into what the AI parses as authoritative page metadata.
Text concealment techniques were the second most observed category. Attackers use CSS to shrink text to 1 pixel, set font color to near-transparent values, or position elements off-screen. The text is invisible to a human viewing the page in a browser but fully legible to an AI agent extracting text from the DOM or raw HTML.
Google specifically warned about agent chaining scenarios. When Agent A reads and summarizes a document, then passes that summary to Agent B for action, an injection planted at the Agent A stage can propagate through the chain and influence Agent B's behavior. Multi-agent architectures amplify the attack surface in ways that single-agent setups do not.
Forcepoint's 10 Payload Families
Where Google's report provides the macro-level view, Forcepoint X-Labs delivers the operational taxonomy. Their researchers identified 10 payload families actively found in the wild, organized by attack objective:
| Rank | Payload Family | Severity | Target |
|---|---|---|---|
| 1 | Financial Fraud (B2B Wire) | Critical | Alter payment instructions, swap account numbers |
| 2 | API Key Exfiltration | Critical | Steal tokens and keys the agent has access to |
| 3 | Data Destruction | High | Delete files, corrupt database records |
| 4 | AI Denial-of-Service | High | Trigger infinite loops, exhaust compute |
| 5 | Privilege Escalation | High | Expand agent permissions beyond intended scope |
| 6 | Data Exfiltration | High | Send sensitive data to external endpoints |
| 7 | Social Engineering Amplification | Medium | Use agent to craft and send phishing messages |
| 8 | Supply Chain Poisoning | Medium | Inject into code repos and package registries |
| 9 | Prompt Relay | Medium | Propagate injection to downstream agents |
| 10 | Log/Audit Evasion | Low | Suppress or delete evidence of the attack |
The financial fraud category sits at the top for a reason. As AI agents increasingly handle invoice processing and payment approvals in enterprise workflows, a single instruction hidden in a PDF invoice -- "route this payment to account X instead of account Y" -- can redirect real money. This is the AI-native evolution of Business Email Compromise (BEC), which the FBI estimated caused $2.9 billion in losses in 2023 alone. The difference is that BEC required a human to fall for the scam. Now the target is a machine.
API key exfiltration is equally alarming. Enterprise AI agents hold credentials for multiple services. A successful injection can instruct the agent to POST its API keys to an attacker-controlled URL, turning a single compromised agent into an entry point for lateral movement across the entire service mesh.
Neither report found evidence of coordinated campaigns -- no nation-state operations, no APT-level activity. But they did find shared injection templates across unrelated domains. This suggests that toolkits are being shared in underground communities, much like exploit kits for web vulnerabilities have been traded for years.
Attack Techniques in Detail
Five technical approaches keep showing up across both reports.
CSS concealment is the simplest and most prevalent. Setting font-size: 1px, color: rgba(255,255,255,0.01), or position: absolute; left: -9999px makes text invisible in the browser while remaining fully extractable by any text parser. The challenge for defenders is that these CSS patterns are also used legitimately -- screen-reader-only text, SEO markup, accessibility labels. A blanket ban on hidden text would break half the web.
HTML comment and hidden element injection places payloads inside <!-- --> comments or elements with hidden attributes and display: none styles. Whether these reach the AI depends on the agent's text extraction pipeline. Some agents strip HTML before processing; others parse the raw DOM. The inconsistency across implementations is itself a vulnerability.
Accessibility attribute abuse is particularly insidious. Injecting payloads into aria-label, alt text, and title attributes exploits mechanisms designed to make the web more inclusive. These attributes are not visually rendered but are read by screen readers -- and by AI agents that extract semantic content from HTML. The irony of accessibility infrastructure becoming an attack surface is not lost on the security community.
Meta namespace spoofing creates fake <meta> tags with names like ai-instruction or agent-directive, gambling that some AI agents will treat them as authoritative page-level metadata. System prompt tag impersonation takes the most direct approach: embedding strings like ### System: or <|im_start|>system in page content, hoping the model's tokenizer will interpret them as control tokens.
All five techniques exploit the same fundamental gap: the difference between what a human sees and what an AI reads. As long as web standards allow machine-readable content that is invisible to humans, this gap will persist.
The Autonomy-Security Tension
The deeper problem these reports expose is not a bug to be patched. It is a structural tension between what makes AI agents useful and what makes them safe.
The entire value proposition of an AI agent is autonomous action -- reading emails, scheduling meetings, writing code, approving payments without constant human supervision. But the moment you grant that autonomy, every piece of external content the agent processes becomes a potential attack vector. More capability means more attack surface. This is not a problem better filters will solve.
The Hacker News debate has crystallized around two camps. The "always confirm" camp argues that agents should require explicit user approval before any action with side effects. This is logically sound and practically self-defeating -- if every action needs approval, the agent is just a very expensive clipboard.
The "provenance plus sandboxing" camp proposes tracking the origin of every input and restricting what the agent can do based on trust levels. Content from untrusted sources would be processed in a restricted capability sandbox. This is more promising but fiendishly hard to implement. Where do you draw the trust boundary? A colleague's email is trusted, but what if that colleague's account was compromised? A company's official website is trusted, but what if it was defaced?
The most honest framing comes from the security researchers themselves: there is no equivalent of parameterized queries for LLMs. SQL injection was solved by physically separating the data channel from the command channel. In an LLM, system prompts, user messages, and external document content all flow into the same text stream. Until model architectures change at a fundamental level, indirect prompt injection will remain a cat-and-mouse game.
The OpenAI Timing
On May 1 -- one week after the Google and Forcepoint reports dropped -- OpenAI pushed a mandatory update for its macOS desktop app, with a hard deadline of May 8. No specific CVEs were disclosed. But the security community notes that the macOS desktop app has system-level access: file system reads, cross-app data transfer, clipboard access. In that environment, a successful indirect prompt injection has a blast radius that extends far beyond the browser sandbox.
The fact that this is a mandatory update -- use is blocked if you do not comply by May 8 -- signals that OpenAI considers the threat credible enough to force the entire macOS user base through an update cycle. The timing alignment with the Google and Forcepoint reports is unlikely to be coincidental.
Stakes -- Wins / Loses / Watching
Wins
- Security research community. Indirect prompt injection just got promoted from "interesting theoretical problem" to "documented in-the-wild threat." Funding, attention, and headcount will follow.
- Enterprise security vendors. A new threat category means a new product category. AI firewalls, injection detection layers, and agent behavior monitoring tools are already being pitched.
Loses
- AI agent startups marketing "fully autonomous" workflows. Adding user confirmation steps degrades the UX. Not adding them is now a documented liability.
- Enterprise IT buyers evaluating agent deployments. Showing these reports to a CISO will slow down procurement cycles.
Watching
- Model-level defenses from Anthropic, Google DeepMind, and OpenAI. Can next-generation models learn to distinguish data from instructions more reliably?
- MCP (Model Context Protocol) standardization. How will security be embedded at the protocol layer for agent-tool interactions?
- EU AI Act enforcement. When indirect prompt injection causes financial harm, who bears liability -- the model provider, the agent developer, or the platform hosting the poisoned content?
What to Do Monday Morning
Agent developers: audit your input preprocessing pipeline today. Check how your agent handles HTML comments, hidden text, meta tags, and accessibility attributes in external content. At minimum, add pattern matching for system prompt tag impersonation. Use Forcepoint's 10 payload families as a checklist and verify your defenses against each one.
Enterprise security teams: inventory every resource your AI agents can access. Email, file systems, APIs, databases -- map the full access graph. Apply the principle of least privilege. If an agent only needs read access, revoke write permissions. Verify that audit logs capture agent actions at sufficient granularity to detect post-compromise behavior.
Everyone using OpenAI's macOS app: update before May 8. If you have AI agents set to auto-process emails or documents, add manual confirmation gates for high-risk actions -- payment approvals, file deletions, credential sharing. The convenience cost is small compared to the risk.
References
- Google Online Security Blog -- AI Threats in the Wild: https://security.googleblog.com/2026/04/ai-threats-in-wild-current-state-of.html
- Forcepoint X-Labs -- Indirect Prompt Injection Payloads: https://www.forcepoint.com/blog/x-labs/indirect-prompt-injection-payloads
- Help Net Security -- Indirect Prompt Injection in the Wild: https://www.helpnetsecurity.com/2026/04/24/indirect-prompt-injection-in-the-wild/
- Decrypt -- Google Prompt Injection AI Agents: https://decrypt.co/365677/google-prompt-injection-ai-agents-paypal-enterprise
- Cybernews -- More Prompt Injection Attacks: https://cybernews.com/ai-news/more-prompt-injection-attacks-ai-agent-google-warn/
관련 기사
Gemini Just Redefined Google Workspace — A Complete Breakdown of the Docs, Sheets, Slides, and Drive Overhaul
Google deeply integrated Gemini across Workspace. Sheets auto-fill is 9x faster, Docs draft from cross-app data, Drive gets AI search. Full specs, benchmarks, and competitive analysis.
Gemini 3.1 Flash-Lite Arrives at $0.25/M Tokens — Inside the LLM Price War That Cut Costs 80% in One Year
Google's Gemini 3.1 Flash-Lite sets a new floor for LLM pricing. Here's how API costs dropped 80% year-over-year, who's winning the price war, and what it means for developers.

42.5 ExaFLOPS: Google's Ironwood TPU Rewrites the Inference Playbook
Google's 7th-gen TPU Ironwood hits GA with 4,614 TFLOPS per chip, 9,216-chip superpods, and Anthropic signing up for 1M TPUs. The inference era has a new king.
AI 트렌드를 앞서가세요
매일 아침, 엄선된 AI 뉴스를 받아보세요. 스팸 없음. 언제든 구독 취소.
